How to Block RFID: Essential Security Strategies for Mac-Based Businesses

In an era where digital theft can happen with a simple walk-by scan, protecting your business’s sensitive data has never been more critical. How to block RFID isn’t just about personal security—it’s about safeguarding your company’s financial assets, employee information, and client data from sophisticated skimming attacks that can occur without you ever knowing.
Radio Frequency Identification (RFID) technology powers everything from contactless payment cards to employee access badges, making our Mac-centric workflows more efficient than ever. However, this convenience comes with significant security risks that creative agencies, small businesses, and Mac-based operations cannot afford to ignore.
Key Takeaways
• RFID blocking requires physical barriers that prevent electromagnetic signals from reaching your cards and devices
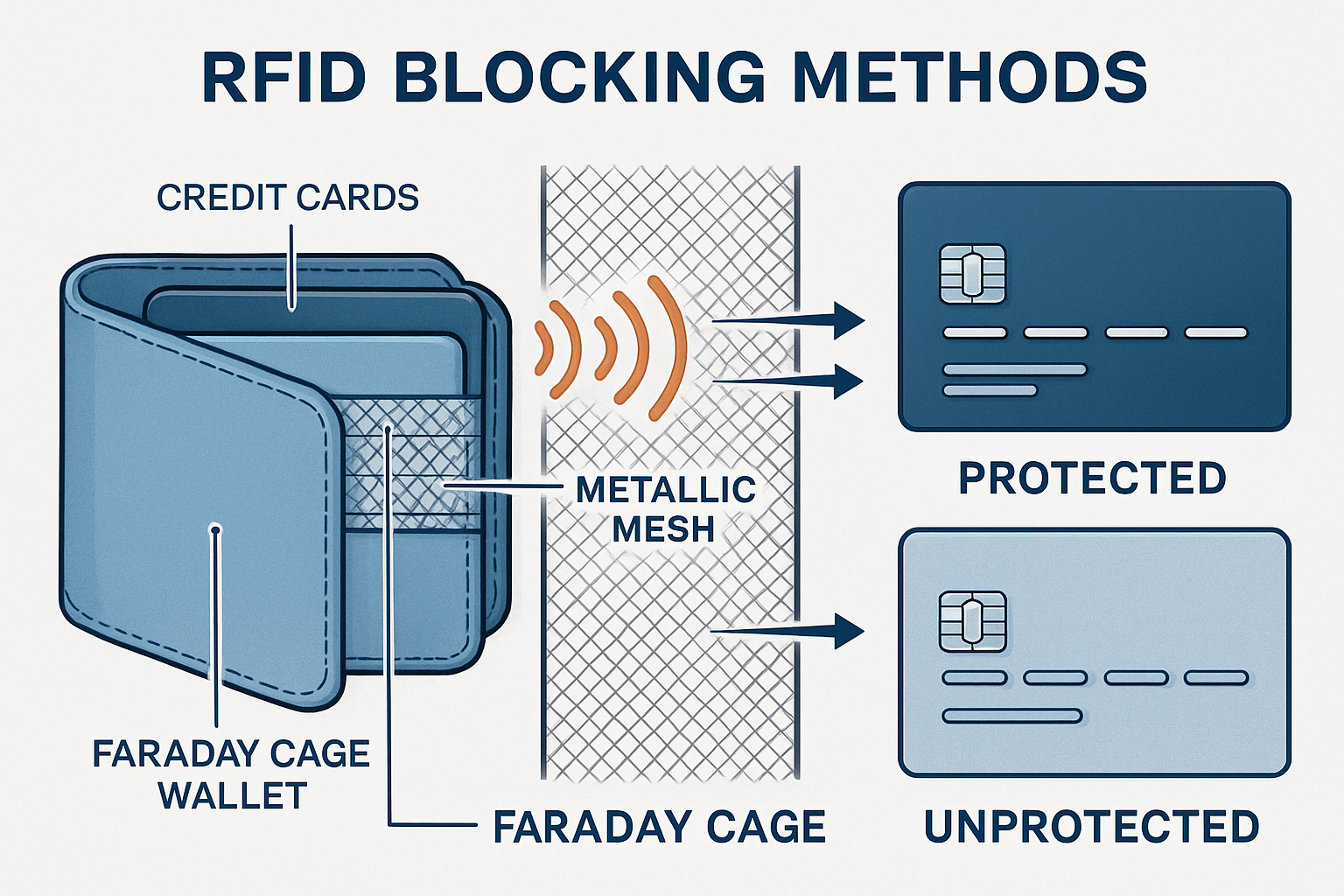
• Faraday cage technology provides the most reliable protection through metallic mesh or foil construction
• Business-grade RFID security involves both individual protection methods and comprehensive access control policies
• Mac ecosystem integration allows for seamless RFID management through built-in security features and third-party solutions
• Proactive protection strategies significantly reduce the risk of data breaches and financial fraud for small businesses
Understanding RFID Technology and Security Risks
RFID technology operates through electromagnetic fields to automatically identify and track tags attached to objects, including the payment cards and access badges your team uses daily. While this technology streamlines many business processes, it also creates vulnerabilities that malicious actors can exploit.
Everyday RFID-enabled items in your business include:
• Credit and debit cards with contactless payment capabilities
• Employee access badges and key fobs
• Passport cards and enhanced driver’s licenses
• Transit cards and parking passes
• Inventory tracking tags
The primary security concern stems from unauthorized scanning—criminals can use portable RFID readers to capture data from your cards and badges from several feet away, often without triggering any alerts or notifications. This silent theft makes RFID skimming particularly dangerous for businesses handling sensitive financial information.
For Mac-based businesses, this risk extends beyond individual cards to encompass the broader security ecosystem. When employees’ payment information gets compromised, it can lead to fraudulent charges on company accounts, disrupted workflows, and potential liability issues that affect your bottom line.
How to Block RFID: Physical Protection Methods
Faraday cage technology forms the foundation of effective RFID blocking. These protective barriers use conductive materials—typically metallic mesh or specialized foils—to create an electromagnetic shield around your RFID-enabled items.
RFID-Blocking Wallets and Cardholders
High-quality RFID-blocking wallets incorporate thin metallic layers that prevent electromagnetic signals from penetrating the wallet’s interior. When selecting protection for your business team, look for wallets that meet military-grade shielding standards and are durable enough for daily professional use.
Essential features to consider:
• Signal attenuation rating of at least 60dB for comprehensive protection
• Durable construction that withstands frequent opening and closing
• Professional appearance suitable for client meetings and business environments
• Multiple card slots to accommodate various business and personal cards
RFID-Blocking Sleeves and Pouches
Individual card sleeves provide targeted protection for high-value cards while maintaining the functionality of other cards. This selective approach works well for businesses that need to balance security with operational efficiency.
These sleeves typically cost less than complete wallet replacements and allow for gradual implementation across your organization. Quality sleeves use the same Faraday cage principles as wallets but focus protection on individual cards rather than entire collections.
DIY RFID Blocking Solutions
For immediate protection or temporary solutions, aluminum foil can provide basic RFID blocking capabilities. While not as elegant or durable as purpose-built solutions, properly applied foil creates an effective electromagnetic barrier.
DIY implementation tips:
• Wrap cards completely in aluminum foil, ensuring no gaps
• Use multiple layers for enhanced protection
• Test effectiveness with your contactless payment terminal
• Replace foil wrapping when it becomes damaged or worn
However, DIY solutions require ongoing maintenance and may not provide the consistent protection that professional-grade products offer. For business environments, investing in dedicated RFID-blocking products typically provides better long-term value and reliability.
Advanced RFID Security for Mac-Based Businesses
Mac users benefit from Apple’s integrated approach to security, which extends to RFID and NFC management through built-in privacy controls and third-party compatibility. Understanding how to enhance your digital security creates a comprehensive protection strategy that goes beyond physical blocking methods.
Apple Pay and Secure Element Technology
Apple’s implementation of contactless payments through Secure Element chips provides inherent protection against many RFID-based attacks. Unlike traditional contactless cards, Apple Pay generates unique transaction tokens rather than transmitting actual card numbers, significantly reducing the value of any intercepted data.
Mac ecosystem security advantages:
• Device-specific authentication requires biometric or passcode verification
• Dynamic transaction codes prevent replay attacks even if data is intercepted
• Remote wipe capabilities protect against physical device theft
• Integration with business security policies through device management platforms
Enterprise RFID Management
For businesses managing multiple Mac devices and access systems, comprehensive RFID security requires coordinated policies and centralized management. Modern Mac device management solutions allow IT administrators to control NFC and contactless payment settings across entire fleets.
Key management considerations:
• Standardized security policies for all business devices
• Regular security audits of RFID-enabled systems
• Employee training on RFID security best practices
• Incident response procedures for suspected compromises
This enterprise approach ensures consistent protection while maintaining the operational flexibility that Mac-based creative businesses require. By implementing proactive risk management strategies, companies can protect against RFID threats while preserving workflow efficiency.
Integration with Existing Security Infrastructure
Adequate RFID protection works best when integrated with your existing Mac security infrastructure. This includes coordinating RFID blocking strategies with password management, two-factor authentication, and device encryption policies.
Consider how RFID security fits within your broader approach to identifying and preventing security threats. A comprehensive security strategy addresses multiple attack vectors simultaneously, creating layered protection that significantly reduces overall risk.
Choosing the Right RFID Blocking Solutions
Selecting appropriate RFID protection requires balancing security needs with practical business requirements. Different solutions work better for various use cases, and understanding these distinctions helps ensure you invest in protection that is actually used consistently.
Evaluating Protection Effectiveness
Signal-blocking performance varies significantly across products, making it essential to verify actual protection levels rather than relying solely on marketing claims. Look for products that specify their attenuation ratings in decibels (dB) and provide independent testing verification.
Testing your protection:
• Use your contactless cards to verify blocking effectiveness
• Test from multiple angles and distances
• Confirm protection works with all your RFID-enabled items
• Regularly retest as products age and wear
Business-Specific Considerations
Creative agencies and Mac-based businesses have unique requirements that influence RFID protection choices. Consider factors like client presentation needs, travel frequency, and the types of sensitive information your team regularly handles.
Professional environment factors:
• Aesthetic compatibility with business attire and client meetings
• Durability requirements for frequent travel and daily use
• Capacity needs for multiple business and personal cards
• Cost considerations for organization-wide implementation
Implementation Strategies
Rolling out RFID protection across your organization requires thoughtful planning to ensure consistent adoption and effectiveness. Start with high-risk individuals—those who travel frequently or handle sensitive financial information—before expanding to the entire team.
Phased implementation approach:
• Pilot program with key personnel to evaluate effectiveness
• Training sessions on proper use and maintenance
• Regular assessment of protection needs as business grows
• Integration with broader security awareness programs
This systematic approach ensures that RFID protection becomes an integral part of your business security culture rather than an afterthought that gets inconsistently applied.
Maintaining RFID Security in Dynamic Business Environments

RFID security isn’t a one-time implementation—it requires ongoing attention and adaptation as your business evolves and new threats emerge. Mac-based businesses benefit from Apple’s regular security updates, but physical RFID protection requires proactive maintenance and periodic reassessment.
Regular Security Audits
Quarterly security reviews should include an evaluation of your RFID protection strategies alongside other security measures. This includes testing the effectiveness of blocking products, assessing new threats, and updating protection methods as needed.
During these audits, consider how changes in your business operations might affect RFID security needs. New payment systems, additional access controls, or expanded travel requirements may necessitate updated protection strategies.
Employee Education and Awareness
Adequate RFID security depends on consistent implementation by your entire team. Regular training sessions help ensure that employees understand both the risks and the proper use of protection methods.
Key training topics:
• Recognition of RFID-enabled items in their daily work
• Proper use and maintenance of blocking products
• Identification of potential threats and suspicious activities
• Integration with existing security protocols and incident reporting
This educational approach builds security awareness that extends beyond RFID protection to encompass broader cybersecurity best practices essential for Mac-based businesses.
Adapting to Technological Changes
The landscape of RFID technology and associated threats continues evolving, requiring businesses to stay informed about new developments and adjust their protection strategies accordingly. This includes monitoring for new attack methods, implementing improved blocking technologies, and adapting to changes in industry standards.
Consider how emerging technologies like ultra-wideband (UWB) and enhanced NFC capabilities might affect your security needs. Staying ahead of these developments ensures your protection remains effective as technology advances.
By maintaining this proactive approach to RFID security, Mac-based businesses can protect their sensitive information while preserving the operational efficiency that drives creative and professional success. Remember that securing your competitive advantage requires attention to both digital and physical security measures.
Conclusion
Understanding how to block RFID effectively protects your Mac-based business from increasingly sophisticated skimming attacks while maintaining operational efficiency. From Faraday cage wallets to enterprise-grade security policies, the right combination of physical protection and digital security creates comprehensive defense against unauthorized data access.
The key to successful RFID protection lies in implementing layered security that addresses both individual and organizational needs. By combining physical blocking methods with Apple’s built-in security features and comprehensive employee training, businesses can significantly reduce their exposure to RFID-based threats.
Take action today:
• Audit your current RFID-enabled items and assess vulnerability levels
• Implement appropriate blocking solutions for high-risk cards and devices
• Integrate RFID security into your broader cybersecurity strategy
• Establish regular review processes to maintain protection effectiveness
For Mac-based businesses seeking comprehensive security solutions that go beyond RFID protection, consider partnering with specialists who understand the unique needs of creative and professional environments. Peace of mind through technology solutions comes from proactive protection strategies that address current threats while preparing for future challenges.
Ready to secure your business against RFID threats and other cybersecurity risks? Contact MacWorks 360 for customized Mac infrastructure optimization, including robust security protocols specifically designed for creative professionals and small businesses. Our 20+ years of expertise in Mac IT support ensure your technology works for you, not against you.
References
[1] Federal Trade Commission. “RFID: What is it, and what does it mean for privacy?” FTC Consumer Information, 2025.
[2] National Institute of Standards and Technology. “Guidelines for Securing Radio Frequency Identification (RFID) Systems.” NIST Special Publication 800-98, 2024.
[3] Apple Inc. “Apple Pay Security and Privacy Overview.” Apple Platform Security Guide, 2025.
[4] Identity Theft Resource Center. “RFID Skimming: Understanding the Threat and Prevention Methods.” Annual Data Breach Report, 2024.

Want this Mac Email Security implemented for you?
MacWorks 360 hardens, monitors, and backs up Mac fleets across New Jersey. We build policies, deploy tools, and prove restores—so your team stays safe and focused.
Contact us · Managed IT for Mac · Apple IT Support
Based in Springfield, NJ—serving Summit, Millburn, Short Hills, Chatham, Montclair, and beyond.